Here are Critical First Steps for a Cybersecurity Assessment
Introduction
For both clients and cybersecurity assessors, the start of an engagement can produce feelings of excitement and anxiousness. There is often the desire to “jump in” to control testing and identification of gaps and enhancements. But the sense of urgency should be resisted until four foundational planning activities occur:
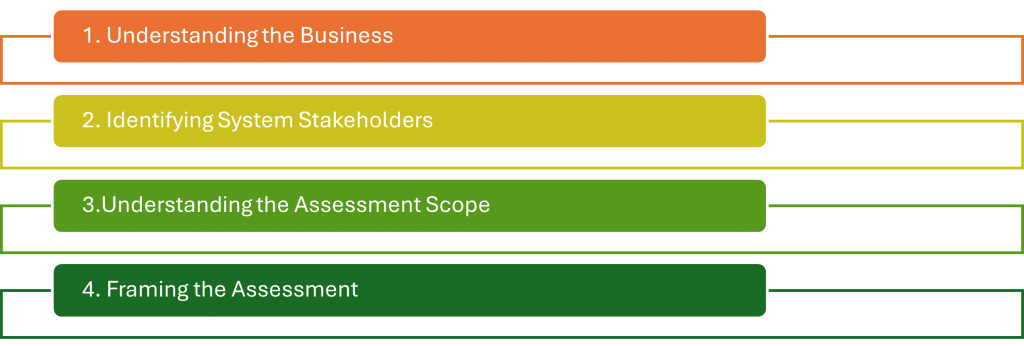
These initial planning activities are assessment critical-success factors and must be performed completely to ensure the efficiency and effectiveness of assessment steps.
1. Understanding the Business
The first key activity is to understand the business. Aside from being a practical step, this requirement is part of the National Institute of Standards and Technology (“NIST”) 800-37 Special Publication, Risk Management Framework for Information Systems and Organizations, A System Life Cycle Approach for Security and Privacy.
Within this framework, Task P-8, “Mission or Business Focus” recommends that organizations identify the mission, business functions, mission / business processes that the systems supports.
Understanding the business includes its mission, business objectives and activities, organizational structure, and locations. This step is critical because, without a thorough understanding of the business, it is difficult to determine how a cybersecurity program and individual systems support and align with the business. It is recommended that this understanding be established early in the assessment process, such as with the initial documents examined and the focus of the initial discovery session.
2. Identifying System Stakeholders
The second key activity is to identify the stakeholders that have an interest in systems or processes under assessment. This foundational step is captured in NIST 800-37 as Task P-9, “System Stakeholders.”
Task P-9 recommends that organizations identify stakeholders who have an interest in the design, development, implementation, assessment, operation, maintenance, or disposition of the systems.
This is a key dependency for the assessment because stakeholders:
- Have the operational and technical expertise needed to understand system risks;
- Uniquely understand how activities connect to mission and business priorities;
- Have the requisite expertise to understand how controls are operating and intended to operate; and
- Are key influencers when it comes to effective, risk-based decision‑making.
Checklist
- Key business owners are identified
- Technical subject matter experts are identified
- Decision-makers for risk acceptance have been identified
- Points of contact have been documented for each in-scope system
3. Understanding the Scope of the Assessment
The third key activity is to understand the scope of the assessment. To fully understand the concept of scope, consider the following. If an organization is having a HIPAA Security Assessment performed, has 100 systems in total but only 10 of those contain Electronic Protected Health Information (“ePHI”), then the scope of the assessment would be those 10 systems and nothing beyond that.
This foundational step is captured in NIST 800-37 as P-11, “Authorization Boundary”. Taks P-11 recommends that organizations determine the boundary or scope of the systems. Without proper scoping, the assessment may be below/beyond what is required and can misrepresent the results with false positive and negative results.
Checklist
- Systems containing regulated or sensitive data have been identified
- Systems excluded from the scope have been identified
- Systems excluded from the scope have a documented rationale
- Assessment scope has been validated by stakeholders
- Any dependencies have been mapped (e.g. shared services or integrations)
4. Framing the Assessment
The fourth key activity is to frame the assessment, known as Risk Framing within NIST’s 800-39 Special Publication, Managing Information Security Risk. This process involves establishing context and provides a common perspective on how organizations manage risk. It includes activities such as risk:
- Assumptions: What is assumed about the threat environment, system usage, dependencies. For example, assuming that all external traffic is routed through a secure gateway may affect how threat likelihood is evaluated.
- Constraints: Limitations that affect risk decisions, such as budget, technology stack, legal and compliance requirements. For example, a constraint may be a legacy system that cannot be updated but must remain operational due to business dependencies.
- Risk Tolerances: How much risk the organization is willing to accept for this system. For example, a financial services company may accept minimal operational risk but have zero tolerance for confidentiality breaches.
- Priorities/Trade-Offs: How the system balances security, performance, cost, and mission impact.
By framing the assessment, organizations are better able to understand how cybersecurity risks and risk treatments (i.e., accept, avoid, transfer or mitigate the risk), are designed to address risk and do or do not align to organizational risk management expectations.
Conclusion
By taking the time to thoroughly complete these four foundational activities, organizations can establish the conditions for a structured and productive assessment.
Myna’s extensive assessment experience can help your organization perform the activities that support a complete, accurate, and value-adding evaluation of cybersecurity and data privacy programs.
Contact our experts today to get started!